
by Pawel Wieczynski
Rising To The Challenge Of Cryptocurrency Crime
Law enforcement nightmare scenario comes true
Imagine a detective’s nightmare: a criminal without fingerprints, able to teleport to any location immediately and wearing a cloak of invisibility. Sounds like pure sci-fi? It shouldn’t. It’s a reality of today’s cyberworld, where criminal networks increasingly recognize the superpowers given to them by the cryptocurrency world.
In 2018 the Bitcoin bubble burst and its value went down by 80%. Some claimed this would mark an end to the popularity of alternative currencies, but that didn’t happen. At the same time it is reported that cryptocurrency trading volumes doubled[1], exceeding the entire 2018 value of US corporate debt trading. Furthermore, it is expected that in 2019 the exchange volume in the crypto world will grow by 50%, enabling it to match the volumes of combined equities traded in the Euro zone[2]!
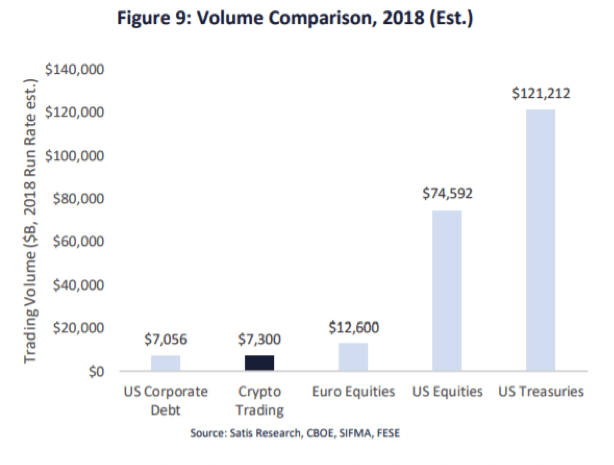
Figure 1: Volume of crypto trading hits $7.3 trillion USD, more than GDP value of Germany and UK combined!
Where is the crypto money flowing?
Out of 11 crypto exchanges analyzed by Reuters[3], the most popular was Bitmex with over $92B of cryptocurrencies traded within a period of 30 days. That is more than the sum of cryptocurrencies traded within 30 days on exchanges ranked 2-4 in this regard: Binance ($32B), OKEx ($27B) and Huobi ($20B).
Bitmex is also the only one of these 11 registered in the “tax haven” Republic of Seychelles; others are registered in Europe, US, Hong Kong, Singapore and South Korea. It is also the only one not performing KYC/AML operations. This may only be the tip of an iceberg, as money coming from criminal activities is washed through an ecosystem of tumblers, gambling sites and payment services.
According to Forbes, cryptocurrencies are widely used for evading sanctions, money laundering, darknet transactions and other cryptocurrency crimes[4]. Even the crypto-world is not safe itself and is a target for cybercriminals, with $1.7 billion stolen in cryptocurrencies in 2018 and 3.6x more hacks on exchanges than in 2017[5]. The dynamic growth of the cybercrime world, with a staggering $6 trillion of cybercrime cost expected in 2021[6] (over 7% of global GDP!!!), is fueled by cryptocurrency trading.
Is there no hope then?
How to shed light on cryptocurrency crimes and the dark side of the financial system?
In principle, analysis of cryptocurrency flows is often possible in the same way as traditional money flows. However for many reasons, such as limited access to data, lack of understanding of how the crypto world works, or technological barriers, only a limited number of investigators and prosecutors are capable of doing it. Yet major economies are beginning to invest into building infrastructure to both capture the data and to enable analytical capabilities for their law enforcement agencies, as not covering this part of the financial flow creates both tax loopholes and a major security threat. According to a Coin Telegraph report, most systems are still in development and will be limited to data coming from cryptocurrency exchanges registered in a particular country[7].
Country | Cooperating with exchanges | Systems for monitoring and identification status | Stores cryptocurrency trades history | Monitors local or global exchanges? |
Japan | YES | In development | YES | Local |
Russia | YES | In development | YES | Local |
United States | YES | Operating, probably most advanced | YES | Global |
China | YES | Operating | YES | Global |
India | YES | Operating | YES | Local |
UK & EU | YES | Unknown, was planned in 2017 | Unknown | Unknown |
Analyzing the crypto trade is just one piece of the puzzle, as there are many ways to effectively hide the identity of traders via multiple tools ranging from the Tor network (“the dark web”), through so called mixers, anonymous crypto currencies as Monero, to anonymizing exchanges such as JoinMarket[8]. This makes investigation of cryptocurrency crimes even more complicated.
Considering the above it becomes obvious that investments in building an analytical environment enabling access to the crypto-world and enabling cryptocurrency crime analysis have to include an effective inflow of data for the most popular cryptocurrencies globally, as well as the ability to enrich these data sets with both internal records and OSINT/Darknet sources. To be effective, such systems must enable big data analytics and, since the crypto-criminals are doing their best to hide their identity, it is critical to use link analytics in order to connect the pieces of data in order to attempt to identify the parties involved in transactions. It is also important for such systems to store the entire available history of crypto-trading, as effective hacking operations can alter the archive data of the crypto-network, as done in the famous 51% attack[9]. Further, identification of wallets from addresses is reliable if computations include the entire historical data sets.
Can we afford to ‘see no evil, hear no evil, speak no evil’?
The conclusion is quite simple: the crypto world has become a part of the global financial system, and as such, has to be included in the monitoring and analytical effort. There is no doubt that the ability to identify and investigate cryptocurrency crime increasingly is a basic requirement for national and international law enforcement agencies.
Even more so, it is important to store the historical data, as the crypto world is increasingly dynamic and look-back analysis of cryptocurrency crimes might in some cases be particularly difficult or impossible.
Tomorrow is here. We’re living in a world where the cybersphere is becoming an increasingly critical area of battle between the good and the bad guys, with cryptocurrencies becoming its cardiovascular system. To prevail in the fight again cryptocurrency crimes, law enforcement must arm itself with the right tools.
DataWalk is a system that provides a Big Data repository with integrated analytics. DataWalk provides the ability to store all relevant cryptocurrency data, and to enrich and complement this with data from various other sources (OSINT, internal sources, etc.) in order to maximize effectiveness of identifying and investigating cryptocurrency crime.
------------------------------------------------------
[1] https://cointelegraph.com/news/huobi-reports-100-percent-increase-in-trading-volumes-in-2018-over-2017
[2] https://research.bloomberg.com/pub/res/d3h2iTlKWIa4FTLKGJsUn3mis5g:
[3] https://research.bloomberg.com/pub/res/d3h2iTlKWIa4FTLKGJsUn3mis5g:
[4] https://www.forbes.com/sites/jasonbloomberg/2019/01/19/the-eight-most-popular-cryptocurrency-transaction-types-are-not-what-you-expect/#310a2f1116ea
[5] https://bitcoinist.com/cryptocurrency-theft-2018-rise/
[6] https://www.forbes.com/sites/sap/2018/01/30/you-need-a-hackers-mindset-to-fight-cybercrimes-6-trillion-price-tag/#5da379884281
[7] https://cointelegraph.com/news/government-tracking-of-crypto-is-growing-but-there-are-ways-to-avoid-it/amp:
[8] https://coinsutra.com/anonymous-bitcoin-transactions/
[9] https://cointelegraph.com/news/ethereum-classic-51-attack-the-reality-of-proof-of-work
Related Posts On The DataWalk Blog
You Might Also Like
Solutions
Product
Partners
Company
Resources
Quick Links


